
As part of our focus on security and has had a security incident ourselves, our friends from Covve are sharing proper security practices with a sharp focus on how you can protect your business from security breaches and how to respond to identity threats. When the average person thinks of identity theft, the most common causes that come to mind are a lost wallet or a stolen credit card.
But, in today’s digital world, that is not all that you should be thinking about. Your digital identity is vulnerable to theft on any device and any site or app you visit – which makes it extremely important to know how to protect your identity.
In more recent times, online abuse is playing an increasingly significant role. While there is no single software or service that can completely eliminate the possibility of identity theft, there are a number of small actions we can take that will greatly reduce our vulnerability. Better education and preparedness can vastly reduce the risk.
This article examines three free services available that will help raise your awareness about any potential vulnerabilities, reduce the risk of harm, and keep you better protected moving forward.
Password Management
1. Recommended Tool: LastPass

It’s best practice to ensure you use strong, unique passwords for all online services and transactions. However, managing all your passwords for each site is near impossible for the average person. Consider using an independent password manager. While there are many services out there that work – Last Pass is a great option. This software will help you generate and use secure, complex, and appropriately long passwords while avoiding the need to remember passwords yourself. Practically speaking, these are things people don’t do unless they have a tool in place to help them.
Why LastPass? LastPass is specifically designed to secure, generate and store unique passwords for every site. LastPass is a host-proof solution, meaning the system is designed to ensure that only the user can access their data. Sensitive data is encrypted locally in a ‘vault’ that is stored on the end user’s device. It encrypts all your passwords and secure information on your computer, using a security key that only you know (appropriately entitled a “master password”). Then, it transmits the encrypted string of characters to LastPass’s online servers.
Because the data is encrypted, it is essentially “scrambled” before it gets sent out over the web. The receiving party has the key to unscrambling it and restoring it to valid information. This way, if the sensitive data is ever intercepted in transmission, the information is useless without the decryption key.
Data Breach Monitoring
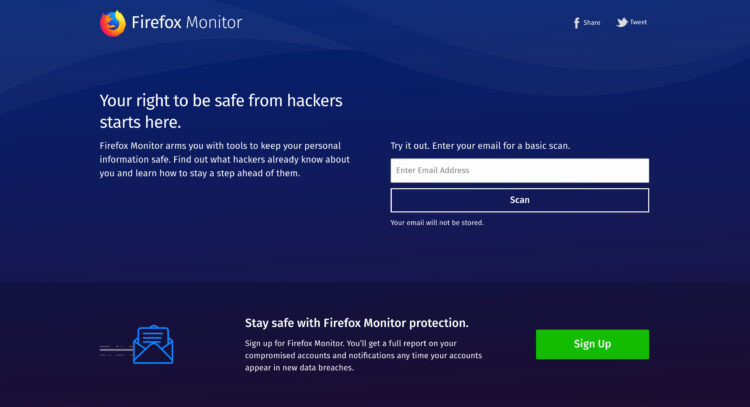
2. Recommended Tool: Mozilla Firefox Monitor
Data breaches and identity theft are rising at an alarming rate, in the past year over 2.6 billion records (that’s billion with a B) were stolen or exposed. These records are often bought and sold on the dark web. What they are after is usually simply passwords.
Since most people do not use a password manager like the tool mentioned above, hackers can obtain a single password and username and use it on various other sites. This becomes dangerous in cases like banking or other sensitive data repositories where these thieves are trying to profit with your information by manipulating accounts. In some instances, they may even try to apply for credit, a mortgage, or a loan with your identity. The consequences are grave for you and your future without properly protecting and monitoring your online presence across sensitive accounts.
Why Firefox Monitor? Mozilla’s free Firefox Monitor service helps you track which of your email addresses have been part of known data breaches. Firefox Monitor warns you if your email address has been exposed and it provides support on how to better protect your online accounts. This service will automatically notify you of what happened and what personal data of yours was included so that you can deduce your level of risk.
Your next steps will depend on what information you need to protect. You need to understand how sensitive the data that has been compromised:
- Least Sensitive: Email addresses, phone numbers, street addresses;
- More Sensitive: Names, dates of birth, card numbers;
- Most Sensitive: Social security numbers, passwords, security codes.
The service shows current as well as past breaches, so you will need to understand when the breach happened. You may receive the notice months or even years after the data breach occurred. Sometimes it takes a while for companies to discover a breach. Other times, breaches are not immediately made public.
Two Factor Authentication
3. Recommended Tool: Google Authenticator

Two-factor authentication (2FA), sometimes referred to as two-step verification or dual-factor authentication, adds an additional layer of security to the authentication process by making it harder for attackers to gain access to a person’s devices or accounts. With single authentication (just a username and password) someone can breach your accounts without knowing solely those two bits of info.
With 2FA, the attacker would essentially need to have access to your phone, computer, or some other additional device to gain entry. While biometric and other super-secure methods are available, the easiest way to set up 2FA is using a software service like Google Authenticator. If you want to dive into the nitty-gritty, this guide will detail everything you need to know.
Why Google Authenticator? If you push your 2FA codes to a text message (SMS) then a sophisticated hijacker may still be able to intercept those codes. However, the benefit of an app like Google Authenticator is that you have all of the codes in a central location that are available all of the time, even when your phone is offline. All you need to do is open the app, grab a secure code (that regenerates every 30 seconds) and you’re in. While this form of authentication is not as secure as biometric or security keys, it is a great first step for the average person to take to add a layer of protection for themself.











