
Cyber security is a big issue in the 21st century. The delights and innovations of social media and technologically innovative solutions have been slightly offset by the risk of data loss, breaches, and hacks. As a matter of fact, whenever you log on to a website via an internet connection, you’re exposed. With every detail you enter while registering on various social media and business platforms, you give out tons of information about yourself.
Visiting the wrong website can inadvertently let a virus onto your device. Even worse, several phishing hacks and thieving websites disguised as payment portals are waiting for unsuspecting victims to enter their credit card details. Over time, these “digital tracks,” as it were, accumulate, and there’s precious little you can do to erase the logs. More often than not, you can barely remember all the platforms you entered your personal details.
Even if you manage to erase a few, chances exist that there are tons of websites and digital brokers out there still holding on to your information. Consequently, it’s now more important than ever to take your data privacy and security seriously. Thankfully, there are many ways to do this and surf the internet anonymously. In this article, you’ll learn seven techniques on how to go about this. Read on to find out!
1. Encrypted Browsers

The truth is many browsers around don’t provide top-level encryption. As a result, data transmissions can be intercepted by third parties unknown to you. Popular browsers like Chrome and Edge still store some traces of your online activity, making them trackable for organizations or individuals with sophisticated resources.
However, certain browsers are more secure and offer end-to-end encryption. For instance, you can beef up your security and web anonymity by using unique browsers like Tor rather than just the “big-name” browser apps. Tor encrypts your online activity and IP address, making you virtually anonymous on the internet.
However, a crucial downside to this browser is that it doesn’t provide the same level of encryption to additional web apps on your device. For instance, you don’t get top-level security with your desktop apps like Facebook, Mail, Zoom, and other PC applications that require an internet connection. To make the encryption comprehensive across all your apps, you need something else – a VPN tool.
2. Virtual Private Networks
Virtual Private Networks, otherwise known as VPN solutions, are a range of cyber security tools that provide a strong level of internet anonymity for privacy-conscious users. A VPN tool works by rerouting your internet traffic through special servers across the globe, virtually altering your IP (Internet Protocol) address.
Hackers identify your device via your IP address, a set of assigned numbers corresponding to your physical location. With a VPN, you can mask your original IP address as the service routes your internet traffic through highly secure servers.
VPN tools have long been the go-to solution for individuals seeking anonymity on the internet. However, you should note that it’s essential to use the right VPN solution, as not all of them offer military-grade encryption.
3. Use a Secure OS

At the base level of all encryption protocols is the operating system (OS). The OS is the foundation for building app programs, encryption protocols, and system capabilities. Data privacy vulnerabilities are either as weak or as strong as the OS your device is based on.
The most popular operating systems like macOS, iOS, Android, and Windows are fairly secure in their own right. However, they offer nothing like the security levels inherent in the Linux operating system. With the Linux OS, your user details are totally secure and cannot be logged by a third party.
4. Encrypted Cloud Storage
Online activity isn’t limited to surfing social media websites and querying Google for news and trends. Cloud storage is also a massive part of this.
Every time you use Google’s productivity tools like Sheets and Docs, you essentially use its Drive cloud service. This service stores your documents, tools, profiles, and credentials in the cloud, meaning that you can access it anywhere and anytime as long as you have an internet connection.
Regarding privacy, most big-name cloud-storage service providers don’t offer anywhere near truly comprehensive data privacy. On the flip side, certain cloud storage providers like ProtonDrive, Tresorit, and Sync provide end-to-end encryption protocols to ensure anonymity and keep your cloud data and documents safe at all times.
5. Proxy Servers

A proxy server is a unique computer that performs intermediary functions between your device and the internet. It functions in a similar fashion to a VPN solution as it assigns its own IP address, thereby masking yours and leaving you free to browse the internet with complete anonymity.
For instance, a proxy server based in Brazil will remotely indicate to potential scammers that you’re in Brazil, even if you’re half a world away in Japan.
6. Go Incognito
Incognito mode is available on many major browsers. It’s a private browsing mode that’s relatively safe and secure, offering total privacy while you surf the net. When you activate the Incognito mode on your browser, your browsing session isn’t tracked, and the browser doesn’t save your data and site cookies. In fact, your entire browsing history is virtually invisible locally.
However, there are some restrictions to its capabilities, as some of your data might still be visible to search engines, websites, and your Internet Service Provider (ISP). To solve this problem, you have to seek an alternative solution.
7. Data Removal Services
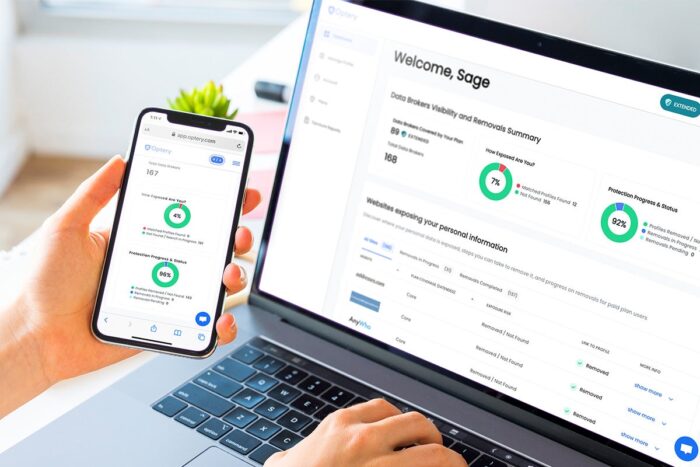
Have you wondered why you get so many ads that seem to match what you usually search for on the internet? It’s because data brokers sell your personal data to digital advertising companies, who then send you ads based on your preferences. While it’s not necessarily a bad idea, it does leave you at risk of identity thieves, hackers, and cyberattacks.
Data removal services such as Incogni help you retrieve your data from these brokers, saving you tons of hours of stress you would’ve otherwise gone through in doing the same. The process is automated, seamless, and guaranteed to give you complete web anonymity in little time.
Therefore, you don’t need to be at the mercy of cyberattacks and unsolicited apps anymore. Instead, take steps to give yourself total browsing anonymity and secure your personal data.











